Cyber attack and skull glowing hologram over working cpu in background. Danger alert, threat, infection and warning abstract concept with skull symbol Stock Photo - Alamy

Cpu On Board With Cyber Attack And Skull Hologram Stock Photo - Download Image Now - Blue, CPU, Computer - iStock
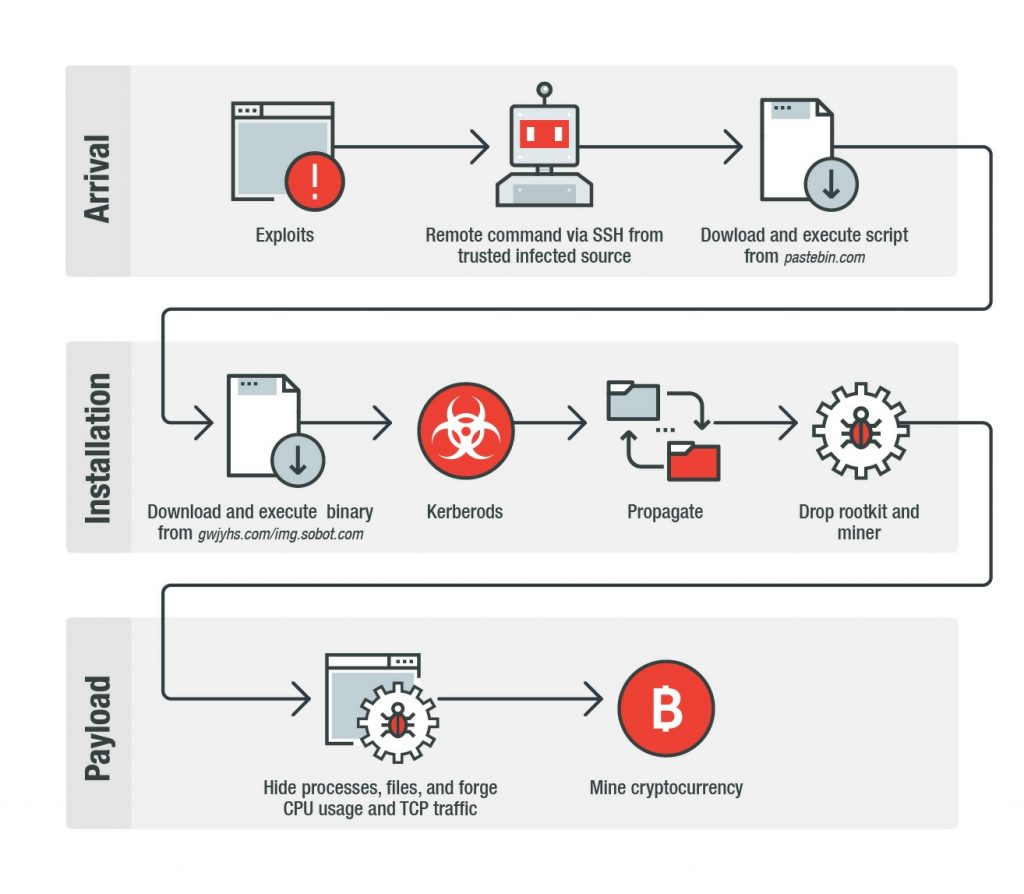
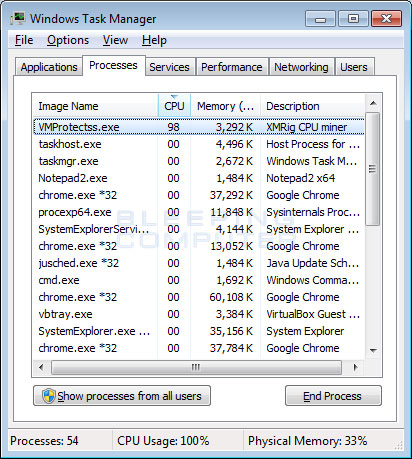
GitHub - Menziess/smbd-cpuminer-infection-fix: A Samba exploit turned Linux into a goldmine. Those infected by the malware would have their systems mining cryptocurrency 24/7, causing their cpu to maintain a 100% usage. My

CPU Virus Infection Spreading Across the Motherboard Stock Illustration - Illustration of connecting, power: 134355324

Cpu on board with cyber attack hologram. Cyber attack hologram over working cpu in background. danger alert, threat, | CanStock

Pichia-secreted mVHH-IgA prevents F4-ETEC infection in piglets a,b,... | Download Scientific Diagram

Valnoctamide Inhibits Cytomegalovirus Infection in Developing Brain and Attenuates Neurobehavioral Dysfunctions and Brain Abnormalities | Journal of Neuroscience

Cyber attack and skull glowing hologram over working cpu in background. Danger alert, threat, infection and warning abstract concept with skull symbol Stock Photo - Alamy