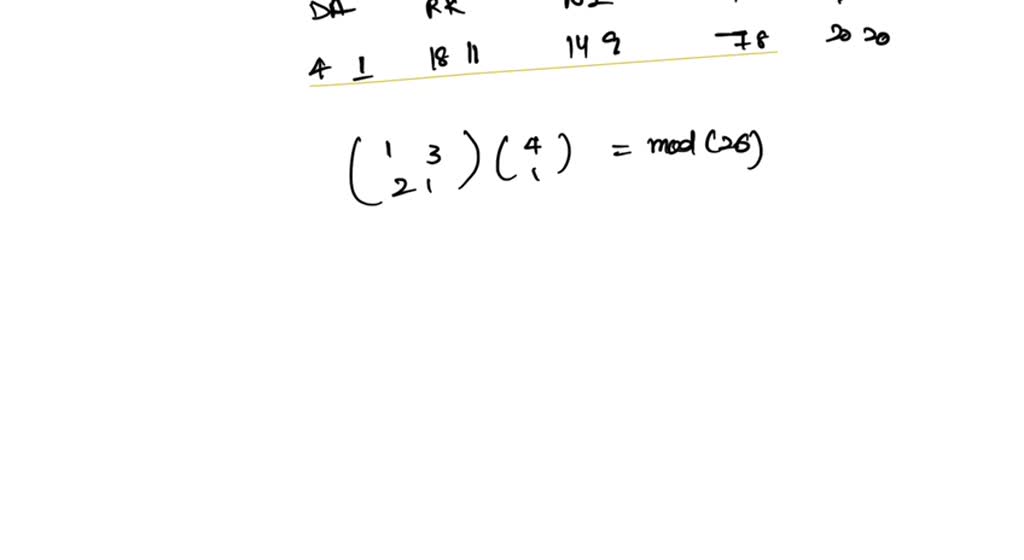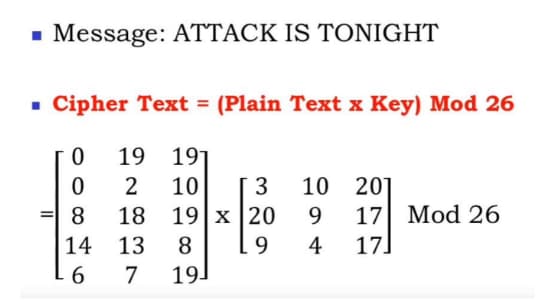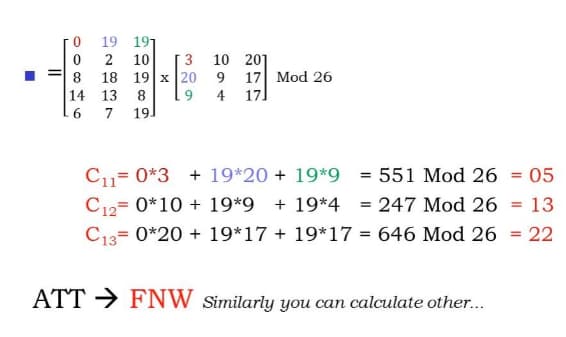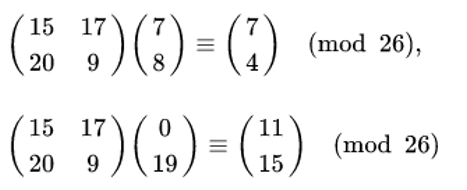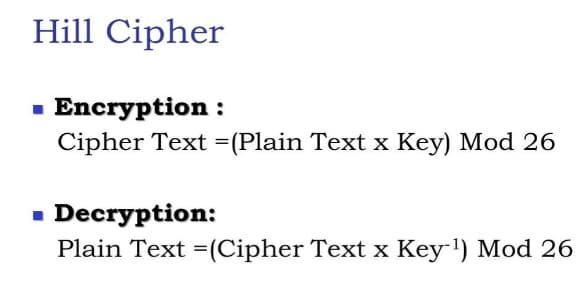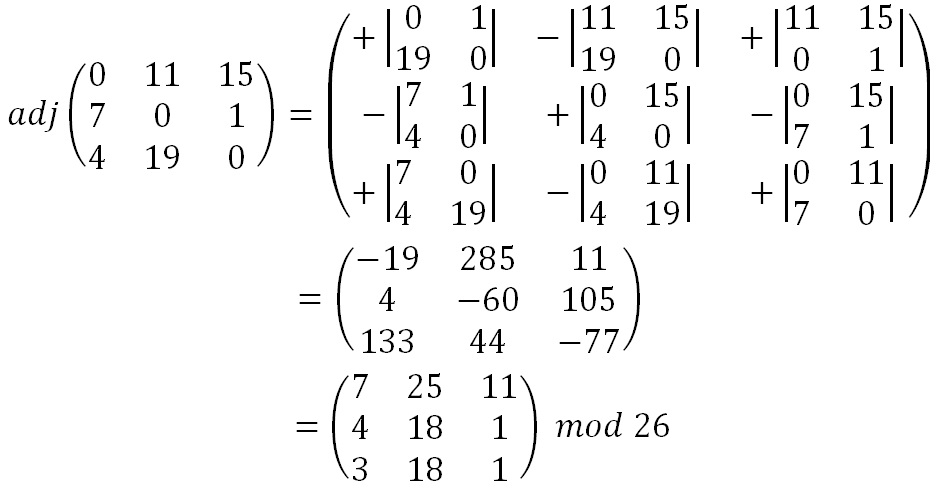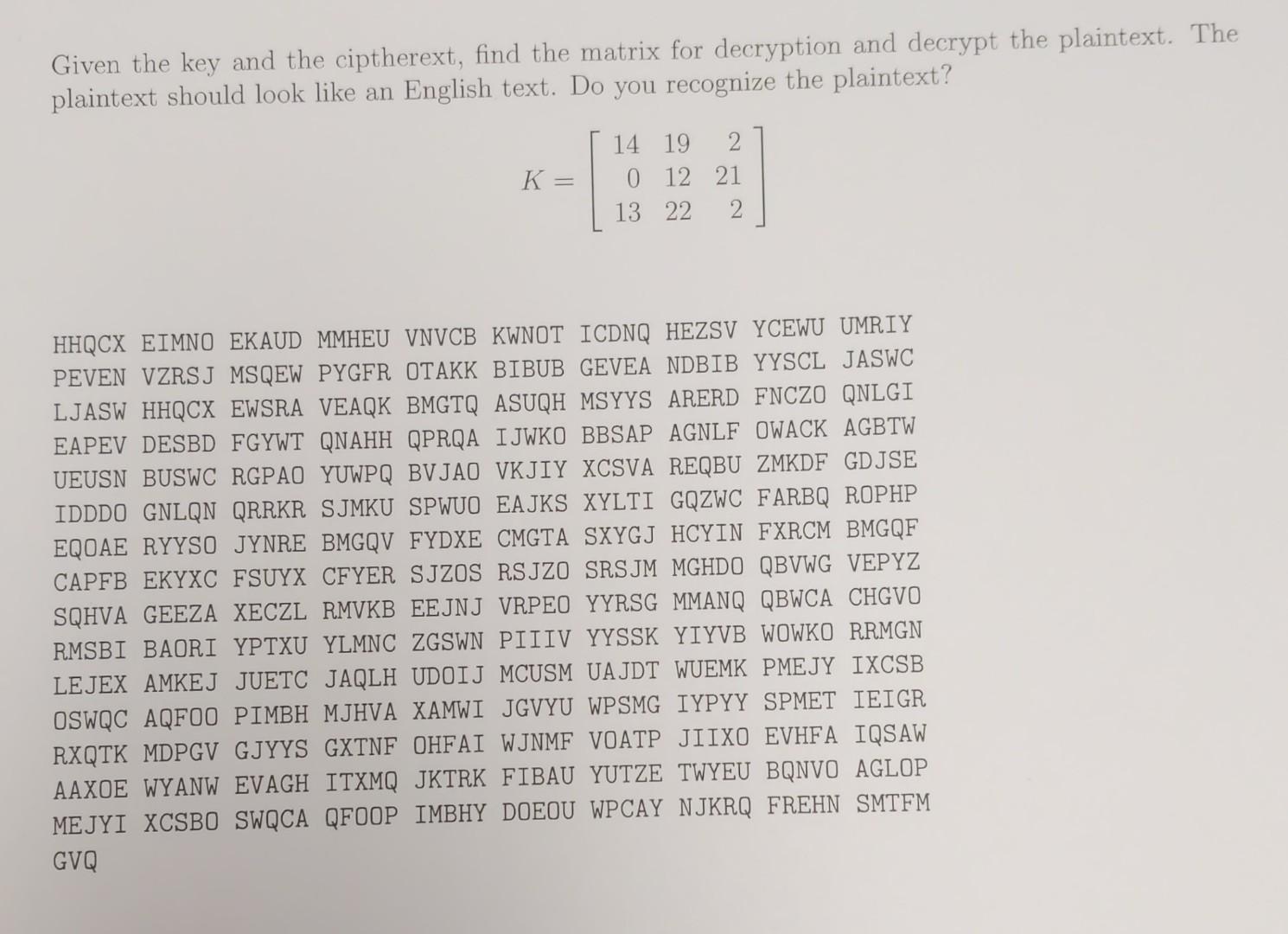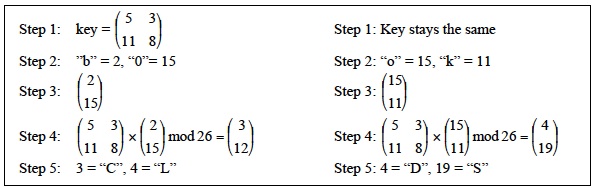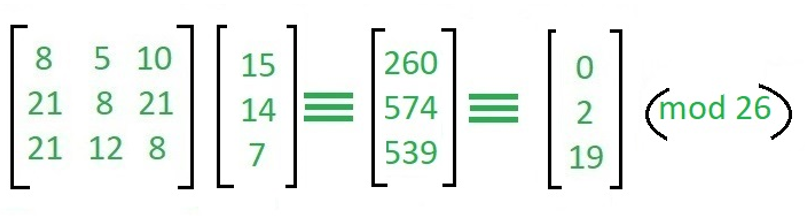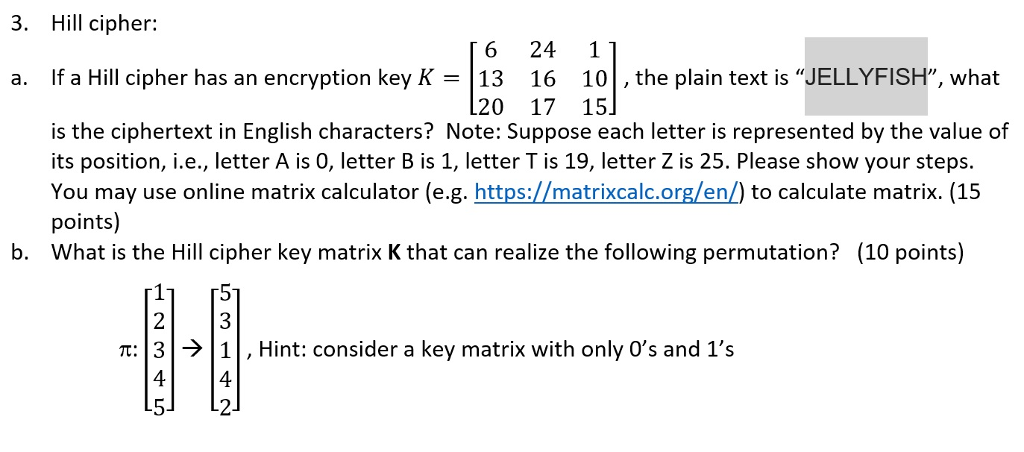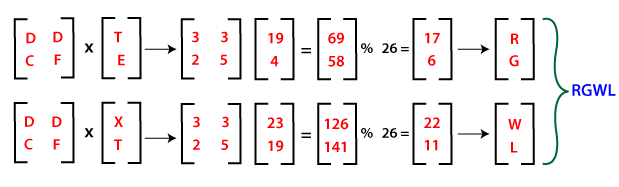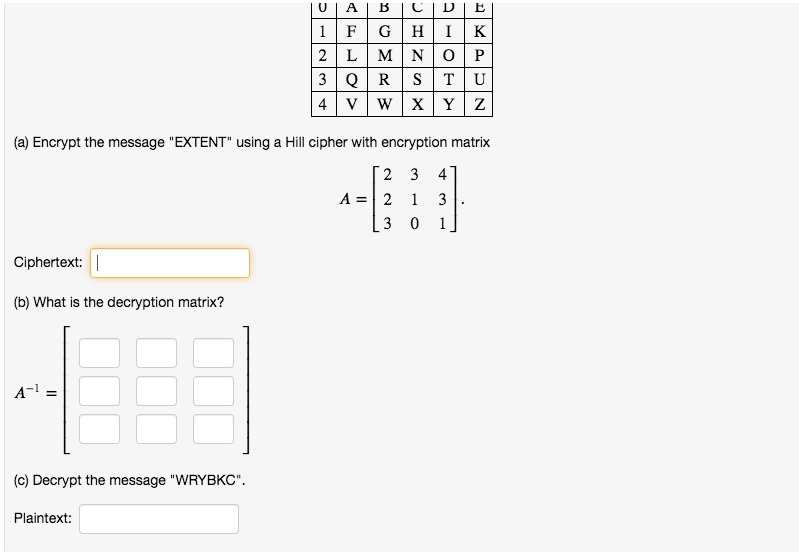
SOLVED: Encrypt the message EXTENT using a Hill cipher with encryption matrix Ciphertext: (b) What is the decryption matrix? A-1 Decrypt the message "WRYBKC" . Plaintext:
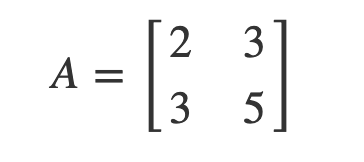
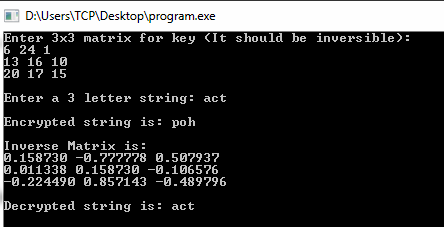
Ciphers and Matrices: The Hill Cipher | by Prof Bill Buchanan OBE | ASecuritySite: When Bob Met Alice | Medium